Something that you can actually remember
Use password manager
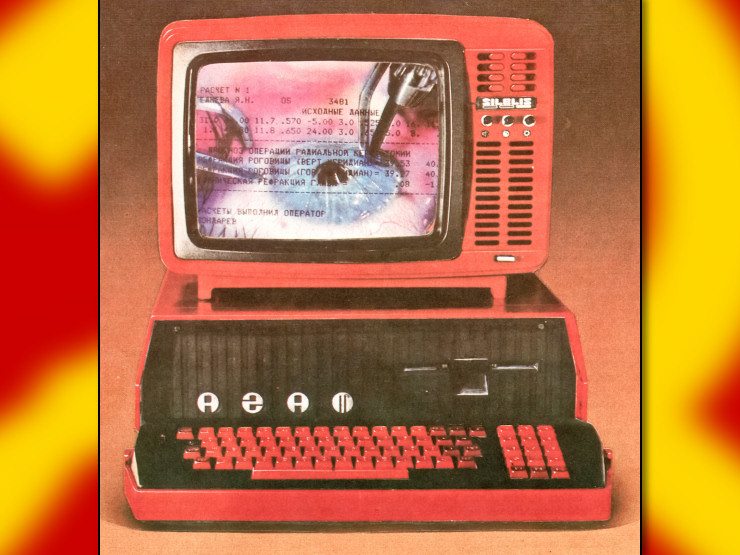
Or this

Weak to dictionary attacks. better make it six words
Ya know that’s what they say, but I’m not so sure - is your dictionary-based brute-forcer doing strings of three words together? Allowing for interspersed special characters between? The sheer character length of three truly random dictionary words in a row is already staggeringly high amounts of entropy - I’m not sure I need to be worried about an attacker capable of that kind of sheer number-buggery.
I’m sure they are ever since this comic came out. It is a very large amount of entropy, but it is still far, far less than an equivalent amount of random characters. Honestly, you do you. If passwords are properly hashed and password attempts are not unlimited and as fast as possible, you’re basically fine.
It’s about combinatorics.
On your bikelock you have a 3 character code with and alphabet of 0-9. So 10^3 = 1000 possible combinations.
If you pick 3 random words out of a dictionary with 40k words, there are 40000^3 possible combinations. (64 000 000 000 000).
Depending on how the password is hashed a 1000$ machine might be able to test anywhere from like 10 to 10 000 000 000 000 hashes per second. (100 billion hashes per second are more realistic)
So a 3 word password might be safe for a very very long time or cracked in seconds.
A 4 word password will take 40000 times as long.
If it’s three words together, they can’t really verify one word by itself. That’s why it’s secure. They would have to test all combinations of three words which would take forever. The reason dictionary attacks work is because people use one word (password), a simple modification of a word (password1!), or a simple common phrase (openssesame1!). The technique is just hoping someone was being ignorant or negligent. But you’re right, they would have to crack all three words in sequence, which means testing all combinations of three words. That’s hard to do.
This is why social engineering is much more important. To even get close to cracking all three words they would have to get to know you, assuming you’re using something related to yourself like a relative’s name, your favorite movie, an inside joke between friends. A targeted attack against you will probably start with social engineering rather than brute forcing your passwords. A random attack is like people who walk down the street looking for an unlocked car door. They’re just trying to find someone who isn’t secure, not you specifically, and therefore probably wouldn’t start with getting to know you.
You want your dictionary to be as small as possible. You can scrape Oxford to a text file and use that, but you’re wasting so much time on thousands of words that are unlikely to be relevant. So rather than just using random words they use common words, phrases, and variations of those in their dictionaries. An actual dictionary probably wouldn’t contain correct, horse, battery, or staple. It’s more likely to be password, password1, password2, etc and then the other common stuff people use for passwords. If you’re a targeting someone specific, you would make a custom dictionary specific to their life.
If you pick 3 randon words out of 40000 that’s less entropy than a 8 random character password with only letters and numbers.
Good info! And that’s exactly what I meant - a word is weak, but several randomized words together is pretty crazy strong. Slightly less than random letters, but much easier to type in memorize when the situation calls for it.
What if you just add a letter after each word. Like correct a horse b battery c staple d.
I imagine single letters are in the dictionary, but that would double the amount of words
or proper nouns that arent in dictionaries
What if you mix languages or do they brute force multiple languages at the same time?
I’ll be real I tried looking up dictionaries used in attacks, ran into the slightest amount of resistance, and immediately stopped caring. Wikipedia has a list of attacks with links if you want to find out yourself
What if I add Tr0ub4dor&3 to my dictionary?
even 4 words with one common substitution fucks up dictionary attack, cause you expand the search space 3-10 fold per word. although one have to have at least one relatively uncommon word (from 20k vocabulary, not 2k vocabulary)
Congratulations, everyone who didn’t say “password manager” just cut down the search space to crack their hexbear.net account password by a huge amount.
I’m p sure hunter2 isn’t in the dictionary
This is a nonsensical criticism. A password of six random words has 2^77 possibilities. This means, even if they knew you were using this method, then with state of the art computing, we’re talking like the age of the universe to crack one. If they didn’t know, then we’re talking like 10^70 times that. A password of just a few words would be more than secure enough.
Search space for cracking passwords, if Hexbear.net is doing any sort of half-decent hashing method, isn’t a very big deal beyond having more than like, 8 characters. If anything, having a common attack vector like a password manager could mean you’re even more likely to be done in.
In a previous life I did a lot of MD5 password cracking, the problem has since been all but solved.
I admit it was a snarky joke from me, and more trying to be provocative about building a security culture than a proper criticism. You’re correct.
(Neat to hear you’ve done some hash cracking in the past!)
I preface this by saying im a tech barbarian and shouldnt be relied on as a reliable source of info on tech topics.
The only bit of advice I remember on password security comes from someone critiquing snowden’s suggestion in some interview where he said the best kind of passwords are pass-phrases like “MargaretThatcheris110%sexy” or some shit and basically said
“MergaretThatcher+is110%PiSSTA” is a whole lot better because it adds more randomness to the mix and makes it harder for the cumputer demons to crack your tough nut of a password open to feast upon its tender innards.
I use a password manager. Most of them have a built in generator that allows you to specify length, type of characters, etc…
I ask my password manager to come up with something. I only have a small number of passwords I actually know, the rest are stored in keepass. I used keepass to come up with my keepass passphrase and the handful of other passwords that I keep in my head.
I dont, password manager makes a real password and remembers it for me
I don’t use passwords that are possible to remember, I use a password manager instead. That’s both easier and more secure at the same time, a hard to beat combo.
Regulatory information off the packaging of something you use and buy frequently.
The caps and punctuation respecting initialization of an article title, publication name and publication date of some bullshit written in a magazine.
The output of a two digit page number, one digit line number, one digit first letter of word number cypher using the isbn of a book multiple times with a one or two digit salt.
Just ask Bitwarden for one and practice it a million times till its muscle memory
Combination of the first letters of road signs and mile markers driving from your home to the nearest state park.
Regulatory information off the packaging of something you use and buy frequently.
WARNING:ThisPasswordContainsChemicalsKnownToTheStateOfCaliforniaToCauseCancer
One thing I find useful with regards to special character requirements: it’s hard to remember a string of special characters, it’s easy to remember a number sequence with the shift key held down.
Password manager.
Then you just have remember one.
correcthorsebatterystaple is the password I use for everything.
Memorize a long sentence, music lyrics, or something 20ish words long, and include punctuation and spaces.
Then if you want to get it extra secure replace some letters with numbers,
Another nugget I’ve heard, is if you include some random chunk in all of your passwords, like “*****” or something, even if it’s predictable, just the sheer character count it adds already gives you a huge boost to entropy. At the end of the day, character count is king. (And the best way to remember long character count strings, especially when they are all unique per service, is a password manager. That’s the actual real secret.)
my master password is a long sentence with a few non-dictonary words in it that mean something to me (one is a compound word one is sci-fi shit). i mix it up sometimes (about every year).
Unless the attacker knows you do that.
Come up with a handful of important main password as a series of very specific words that would be hard to guess. Throw a proper noun in there and don’t make it a well-known phrase.
Important main passwords are those you need to personally remember for important accounts. Like a password manager’s master passwoed, an encrypted document or backup password, or an email account.
For every other password, use an open source password manager where you control the vault. Use the built-in generator to make strong passwords that conform to whatever requirements the service has. If you don’t have the capacity to control your own vault, use bitwarden and work on getting that capacity, then run your own bitwarden or vaultwarden later.
I’d also add that intentional misspellings of words can slow down dictionary attacks, particularly if you use uncommon letter pairings, like HamsterDance -> Hamqter Dpnce.
Use this as a main password (at least 6 words) and then get a password manager (Bitwarden or KeePassXC) to generate the rest.
Don’t come up with the words yourself, roll the dice till you find one you can remember.